This is Domain Histories — a weekly series mapping startup domains from first principles. The best founders are students of history. Patrick Collison met Visa's founder before building Stripe. Apoorva Mehta studied Webvan's collapse before building Instacart. They used history to make specific decisions about what to build, what to avoid, and when to move. Each issue takes one domain and gives you the full map: who tried before, why they failed, where the money sits, what's shipping now, and what a founder entering today should do differently because of it. Not a market overview. Not a research report. The history that changes what you build.
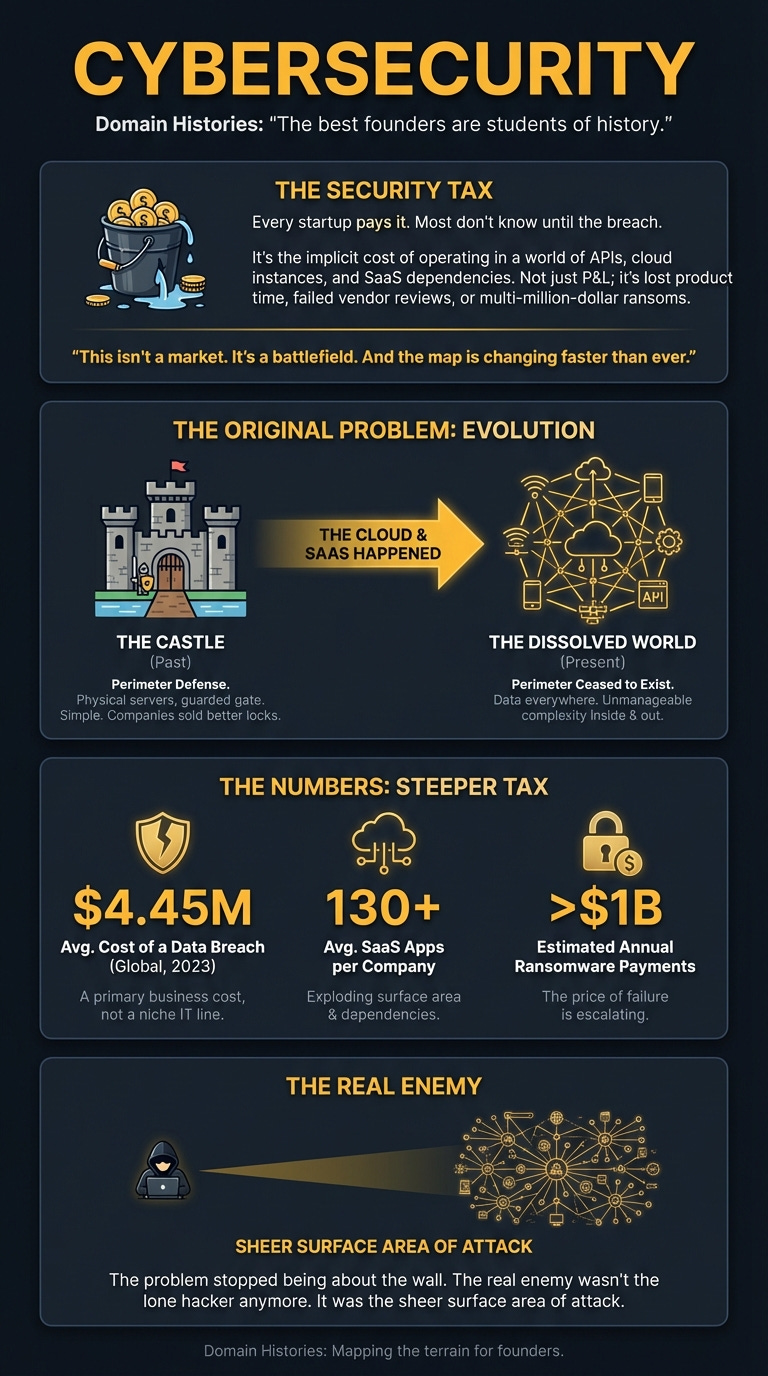
Every startup pays a security tax. Most don’t know until the breach.
It’s not an item on your P&L. It’s the implicit cost of operating in a world where your entire business is a string of APIs, cloud instances, and SaaS dependencies. It’s the time you don’t spend on product because you’re patching a vulnerability. It’s the deal you lose because you can’t pass a vendor security review. Or it’s the multi-million-dollar ransom you pay when it all goes wrong.
This isn’t a market. It’s a battlefield. And the map is changing faster than ever.
The Original Problem
I used to think cybersecurity was about stopping hackers. Black hats in hoodies trying to break through your firewall. A digital game of cops and robbers.
Turns out, that’s a dangerously simple view.
The original problem wasn’t the hacker; it was the castle. For decades, security was about building a perimeter. A strong wall, a deep moat, a single guarded gate. Your servers were in a room you could physically touch. Your employees were in an office you could badge them into. Life was simple. Companies like Check Point became giants by selling better locks for the gate.
Then the world dissolved.
The cloud happened. SaaS happened. Remote work happened. Your data was suddenly everywhere. Your applications were running on someone else’s computers, connected by a thousand different services. The perimeter wasn’t just breached; it ceased to exist.
The problem stopped being about the wall. It became about the dizzying, unmanageable complexity of everything inside. And outside. And in between. The real enemy wasn’t the lone hacker anymore. It was the sheer surface area of attack.
The Numbers
The security tax is getting steeper. The numbers don’t lie. This isn’t a niche IT budget line; it’s becoming a primary business cost.
The Timeline
The evolution of cybersecurity isn’t a straight line. It’s a series of reactions. Each era is a response to the failures and limitations of the last.
Era 1: The Fortress Builders (Pre-2015)
Before the cloud became the default, the game was about protecting the network. The playbook was simple: build a perimeter and defend it.
What Enabled It: A world of on-premise servers and centralised offices. The attack surface was known and finite.
The Playbook: Sell firewalls, VPNs, and intrusion prevention systems. Sell to the Head of IT. Price it as a capital expense, an insurance policy.
Key Company: Check Point Software. Founded in Israel, they were one of the pioneers of the firewall. They built an incredibly durable business by being the best at protecting the castle gate. Even in Q3 2025, they were still pulling in $678 million in revenue with eye-watering 88% gross margins. They are a monument to the profitability of the old model.
Why It Ended: The castle walls dissolved. AWS, Google Cloud, and Azure arrived, and developers started swiping credit cards to spin up infrastructure. The perimeter became a fantasy.
For Founders Today: Don’t underestimate the incumbents. They are slow, but they print money and have deep customer relationships. Your “disruption” is an annoyance to them until it threatens a core revenue stream. They have the cash to wait, watch, and acquire.
Era 2: The Tool Sprawl (2015-2020)
As the world moved to the cloud and DevOps, a thousand new security gaps appeared. This chaos created an opportunity for a new generation of startups.
What Enabled It: The explosion of cloud infrastructure, microservices, and CI/CD pipelines. Every new technology created a new vulnerability.
The Playbook: Pick one painful, specific problem and build a best-in-class tool for it. Developer security. Vulnerability management. Container security. Raise huge amounts of venture capital to fund a land-grab sales motion. Sell to the CISO, who was now overwhelmed.
Key Companies:
Snyk (2015): Focused on finding and fixing vulnerabilities in open-source code, right in the developer’s workflow. A brilliant wedge. They raised a staggering $1.2 billion in total.
Rapid7: A leader in vulnerability management and security operations, helping companies make sense of the flood of alerts. They went public and grew into a major player.
Why It Ended: The cure started to feel like the disease. A CISO might have 50+ different security tools. Managing the tools became a bigger headache than the problems they solved. This created “alert fatigue” and massive complexity.
For Founders Today: A great tool is no longer enough. The market is littered with clever point solutions that never became businesses. If your product doesn’t have a clear path to becoming a platform, you risk becoming a feature for an incumbent to build or a small acquisition for a bigger player.
Era 3: The Platform War & The Wiz Effect (2020-Present)
The pendulum swung back from niche tools to unified platforms. The new battleground wasn’t a single vulnerability; it was providing a single source of truth for the entire cloud estate.
What Enabled It: CISO burnout from tool sprawl. The sheer scale and complexity of public cloud environments made a unified view a must-have, not a nice-to-have.
The Playbook: Build a comprehensive platform that identifies and prioritises risk across a company’s entire cloud infrastructure. Don’t just find problems; show which ones actually matter. Sell the vision of consolidation and simplicity. Move insanely fast.
Key Company: Wiz (2020). The founders, who had previously sold a company to Microsoft, understood the cloud security challenge intimately. They built a platform to scan entire cloud environments for vulnerabilities, misconfigurations, identity issues, and more. Their timing was perfect. In just five years, they were acquired by Google for $32 billion.
What It Means: This exit changed everything. It wasn’t just a massive number; it was proof. It proved a security startup could achieve one of the largest software exits in history, and do it in half a decade. Investors now have a new playbook. The “Wiz effect” means the expectation has shifted from building a tool to building a multi-billion-dollar platform.
For Founders Today: The bar has been raised. Can you consolidate three or four existing tool categories into one elegant platform? That’s the question VCs are now asking. The opportunity is enormous, but the ambition has to match.
The Graveyard
Failure in this space is rarely a single, catastrophic event. It’s a slow fade. It’s the moment when hyper-growth stalls and the market narrative moves on without you.
Where The Money Sits
The money in cybersecurity sits with whoever can reduce complexity and fear.
The value chain is fragmenting and reconsolidating at the same time. You have the Incumbents like Check Point, who own the legacy budgets and are incredibly profitable. They are the defensive bedrock. Their blind spot is speed and the architecture of the modern cloud.
Then you have the Platform Challengers like Wiz, who are eating the world from the cloud outwards. They sell a vision of consolidation to the CISO, promising to replace 5-10 other tools with their one subscription. This is where the venture money is flooding.
Finally, there’s the Security Tax. This is the money every company is forced to spend, either proactively on tools and staff, or reactively on incident response and fines. The global spend is projected to hit $454 billion in 2025. This isn’t a market you create; it’s a tax you help companies manage more efficiently. The opportunity is to turn that tax from a cost centre into a predictable, manageable operating expense.
What’s Actually Hard
Building a security product is hard. Building a security business is harder. Here’s what founders discover 12 months in:
Selling to Fear is a Double-Edged Sword: It gets you the meeting, but it makes you a discretionary budget item. When the economy tightens, the “nice-to-have” security tool that protects against a hypothetical threat is the first to go. The winners sell ROI and efficiency—”we can replace three of your other tools and save you money.”
The Growth Treadmill is Brutal: Snyk’s story is the perfect example. They were a massive success by any normal metric. But they raised money at a valuation that demanded perpetual, accelerating growth. When it slowed to ‘only’ 25%, the narrative soured. You’re not just judged on your performance, but against the expectations your funding created.
The CISO is the Buyer, but the Developer is the User: You have to win over both. The CISO signs the cheque, but if developers don’t adopt and use your tool, you provide no value and you won’t get renewed. This requires a product with both enterprise-grade reporting and a developer-friendly UX. It’s two different products in one.
What’s Shipping Now
The market is moving in real-time. The last six months show a clear divergence:
October 2025: Check Point, the old guard, smashes its Q3 earnings forecast. The stock jumps. They are proving that profitability and stability are back in favour.
January 2026: A Citi Ventures report highlights the “Wiz effect,” confirming that the investment landscape has fundamentally shifted towards platform plays in the wake of the Google acquisition.
February 2026: Rapid7 reports its 2025 results. Revenue is up slightly, but their conservative outlook for 2026 sends the stock plunging. They explicitly mention budget caution and longer sales cycles.
The signal is clear: the market is rewarding profitable incumbents and game-changing platforms while punishing growth-stage companies that show signs of slowing down.
Where This Goes
The next 24 months will be defined by one word: consolidation.
The CISO’s office is ground zero. They are tired, understaffed, and overwhelmed by the sheer number of vendors calling them. The pressure to consolidate tools and vendors is immense.
This creates two paths to victory:
Become a Platform: Be the company that acquires the point solutions and integrates them into a single, cohesive offering.
Be Acquired: Build the best-in-class tool for a specific, painful problem and become an irresistible target for an aspiring platform.
The bet isn’t just on cloud security anymore. It’s on who can build the “Wiz for X”—the definitive security platform for AI development, for IoT, for industrial control systems. The playbook has been written. Now it’s about applying it to the next frontier of complexity.
Moves Worth Stealing
The Fortress (Check Point): Don’t chase growth at the expense of your margins. Build a durable business with a product customers can’t rip out. Focus on net dollar retention and gross margin. It’s not sexy, but it creates a company that can weather any storm and print cash for decades.
The Hyperscale (Wiz): Attack a new, chaotic, and massive market with a 10x better solution that simplifies everything. Don’t build a feature; build a platform from day one. Your goal isn’t to get a slice of the budget; it’s to become the budget. This requires perfect timing, a veteran team, and insane ambition.
The Recalibration (Snyk/Rapid7): When the market shifts, listen. When growth slows and sales cycles lengthen, you have to change the game. Shift the focus from top-line growth to operational efficiency. It’s a tough pill to swallow, especially after raising at a huge valuation, but it’s about survival. The companies that make this pivot will live to fight another day.
The Why Now
One number: $32 billion.
Google’s acquisition of Wiz in 2025 wasn’t just another tech exit. It was a starting pistol for a new era. It proved that the security market is not just a multi-billion dollar opportunity, but a tens-of-billions dollar opportunity for a single company.
The timing signal is this: the first wave of cloud adoption is over. We are now deep in the second wave: the complexity crisis. The pain of managing sprawling cloud environments is now greater than the pain of migrating to them. The person who solves that complexity crisis wins the next decade of security. The window is open right now.
If You’re Starting Monday
The Wedge: Don’t build another vulnerability scanner. Find a deeply unsexy problem created by the intersection of three different cloud services that no one wants to touch. For example, managing ephemeral identities for serverless functions that access a third-party data API. Be the undisputed best in the world at solving that one, painful thing.
The Trap: Building a “dashboard.” A tool that just shows more problems without prioritising them or solving them is just more noise. You will be ripped out in the first budget review. You must automate, remediate, or ruthlessly prioritise.
The Customer: A Head of Security at a 500-person, cloud-native company. They are technical enough to appreciate a good product but senior enough to have budget. They are experiencing tool sprawl firsthand and are desperate for a solution that simplifies their life.
The First Hire: Not a salesperson. A security engineer who has spent the last three years on the receiving end of security alerts at a fast-growing tech company. They know which alerts matter and which are bullshit. They will be your product’s north star.
Go Deeper
The ‘Wiz Effect’: Israeli Cybersecurity is Entering a New Era of Scale — On how the $32B Google acquisition changed the ambition for security startups.
Official 2026 Cybersecurity Market Report — The raw numbers behind the $454 billion market.
Snyk Finds Itself at Crossroads As Its IPO Prospects Dim — A cautionary tale on the perils of hyper-growth and sky-high valuations.
Check Point Software Q3 2025 Earnings Transcript — A look under the hood of an incumbent that still prints money.
Rapid7 Shares Plunge on Weak Outlook — How market headwinds and budget caution can hit even public security leaders.
For the ❤️ of startups
Arthur is the AI native startup operating system I’m building in public — not hype, but a system that turns input into structured execution and tracks founder progress. If you want to follow or use it, it’s open for early access.
→ Access Arthur
Thank you for reading. If you liked it, share it with your friends, colleagues and everyone interested in the startup Investor ecosystem.
If you’ve got suggestions, an article, research, your tech stack, or a job listing you want featured, just let me know! I’m keen to include it in the upcoming edition.
Please let me know what you think of it, love a feedback loop 🙏🏼
🛑 Get a different job.
Subscribe and follow me on LinkedIn or Twitter to never miss an update.