This is Domain Histories — a weekly series mapping startup domains from first principles. The best founders are students of history. Patrick Collison met Visa's founder before building Stripe. Apoorva Mehta studied Webvan's collapse before building Instacart. They used history to make specific decisions about what to build, what to avoid, and when to move. Each issue takes one domain and gives you the full map: who tried before, why they failed, where the money sits, what's shipping now, and what a founder entering today should do differently because of it. Not a market overview. Not a research report. The history that changes what you build.
You have 200 passwords. The industry that created that problem wants to sell you the solution.
Here’s the thing. The chaos of digital identity — the endless logins, the data breaches, the feeling that you’ve been copied and pasted across a thousand databases you’ll never find — isn’t the result of some grand, malicious plan.
The original sin of digital identity was a lack of one.
The Original Problem
The internet wasn’t built for people. It was built for machines to talk to each other. Identity was an afterthought, a patch. When services needed to know who you were, they did the simplest thing possible: they asked you to create a username and a password.
Every. Single. Time.
Each new service built its own little castle with its own little gate. Your bank, your email, your social network, your pizza delivery app. Hundreds of castles, hundreds of keys. This created two massive problems that define the market to this day.
First, a usability nightmare. You, the user, were forced to become a human keychain, juggling hundreds of credentials. Or, more likely, you just used the same password everywhere, turning one leaky castle into a catastrophic failure of the entire kingdom.
Second, a massive, fragmented attack surface. Your identity wasn’t a single thing you owned; it was a thousand little pieces of you, scattered across servers you had no control over. A goldmine for hackers and a business model for the data brokers who figured out how to stitch it all back together and sell it.
The Numbers
The Timeline
The history of identity is a story of bolting on solutions, with each new layer creating new problems. It unfolds in three acts.
Era 1: The Gatekeepers (Pre-2016)
Before 2016, identity was a free-for-all. Every company rolled their own login system. The dominant players weren’t tech companies; they were the old-guard credit bureaus — TransUnion, Experian, Equifax. They quietly built empires by aggregating offline data and selling it back to businesses as a proxy for trust. Their business was, and still is, data arbitrage. They profited from the fragmentation because they were the only ones with a semi-complete picture.
Startups in this era mostly tinkered with Single Sign-On (SSO), trying to create a master key for all your digital locks. But adoption was slow. The problem wasn’t seen as urgent enough to solve.
Why it ended: A European regulation lit a fire under the entire industry.
What it means for you today: The DNA of this era persists. The incumbents still hold the most data, and the default behaviour for any new app is still to build its own siloed identity system.
Era 2: The Compliance Gold Rush (2016-2024)
The General Data Protection Regulation (GDPR) changed the game. Suddenly, mishandling user data wasn’t just bad practice; it was a business-ending liability with massive fines.
Fear became the product.
This shift created companies like OneTrust. Founded in 2016, it was perfectly timed. It didn’t sell a better user experience. It sold certainty to corporate lawyers. It was a compliance engine, a suite of tools to manage consent, map data flows, and generate reports to keep regulators happy. It worked. OneTrust grew into a multi-billion dollar company by focusing entirely on the enterprise’s pain, not the user’s.
The playbook was simple: find a regulatory threat and sell the antidote. The low-hanging fruit of compliance has been picked. Building another cookie-banner tool is a death wish.
Why it ended: Compliance became table stakes, and a new technological wave — AI — introduced a level of complexity that basic compliance tools couldn’t handle.
What it means for you today: Regulation is the most powerful catalyst in this market. If you’re not tracking global data and AI policy, you’re flying blind.
Era 3: The AI Reckoning & Consolidation (2025-Now)
I used to think AI would disrupt the old data gatekeepers. Turns out, it’s their new favourite weapon. Incumbents like TransUnion and Experian are aggressively rebranding as “AI-driven powerhouses,” using machine learning to “weaponize proprietary data.” Their revenue is growing, not shrinking. They’re using AI to strengthen their grip, offering more sophisticated fraud detection and credit scoring than ever before.
This forces the market to evolve. The problem is no longer just privacy compliance; it’s AI governance. How do you prove your AI models aren’t biased? How do you manage the data they’re trained on?
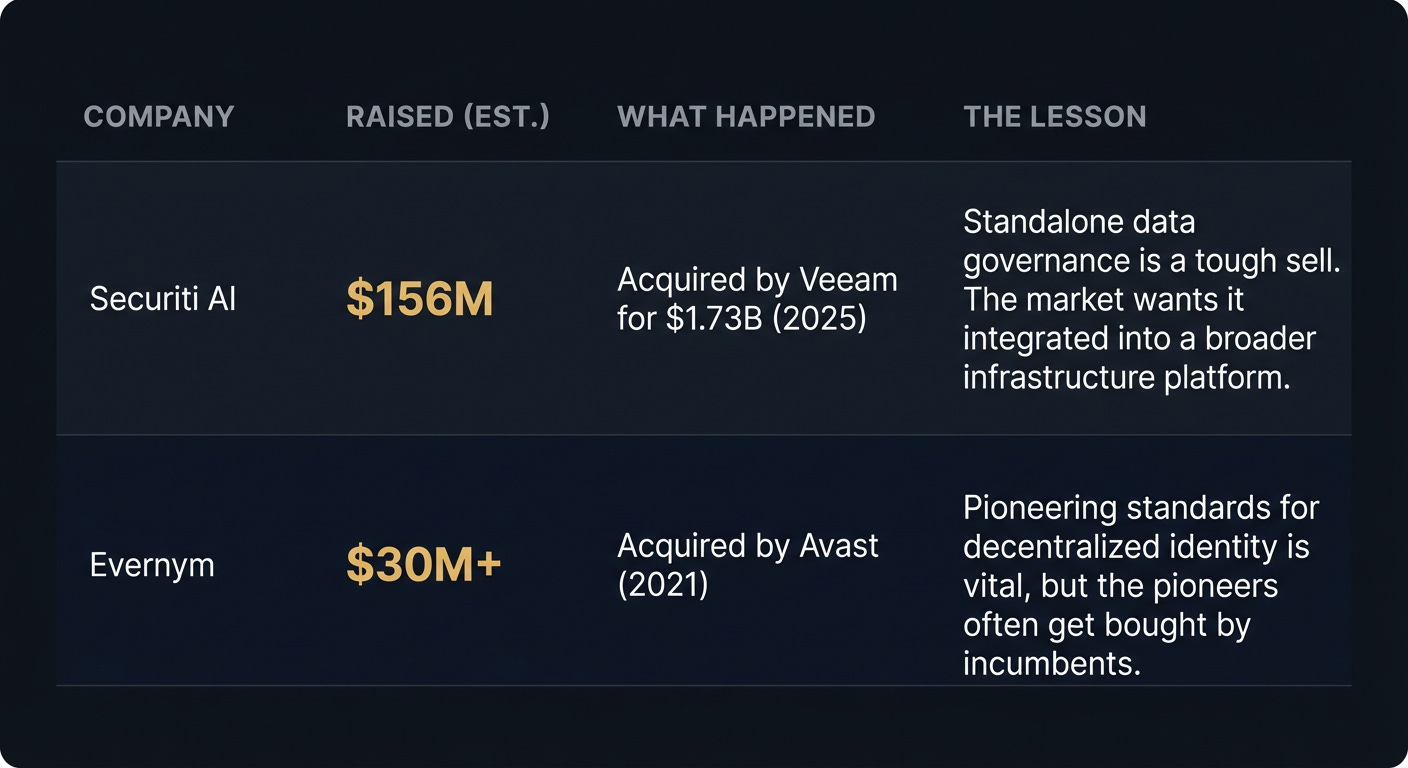
Simultaneously, the market is consolidating. Fast. The cybersecurity space saw a record $96 billion in M&A in 2025. Standalone privacy and identity features are being absorbed into bigger platforms. Securiti AI, a data governance startup, was acquired by infrastructure giant Veeam for $1.73 billion in 2025. It became a feature.
What it means for you today: Competing with incumbents on data is a losing battle. Your advantage has to be in building integrated, trustworthy infrastructure that they can’t — because their business models and legacy tech are too siloed.
The Graveyard
Failure in this space often looks like a successful acquisition. Standalone companies get absorbed into larger platforms, becoming a feature, not a business. The lesson isn’t that they failed, but that building a venture-scale, independent identity company is brutally hard.
Where The Money Sits
The money sits with the gatekeepers: TransUnion, Experian, Equifax. They hold the foundational datasets on billions of people. They profit from complexity, selling access, verification, and analytics back to every other business. Their moat is a labyrinth of proprietary data, regulatory capture, and enterprise sales teams that have been in place for decades.
They are not just data brokers anymore. They are AI companies. TransUnion’s revenue grew 13% in 2025. They are successfully layering AI on top of their core asset — data — to create new, high-margin products.
The tax everyone pays is the “trust tax.” Every time a business needs to verify a user, they pay one of these giants. Every time a new regulation appears, consultants and software vendors get paid to help navigate the complexity that the incumbents thrive on.
Their blind spot? They are slow, siloed, and their products are built for their own benefit, not the user’s. They are trying to bolt on privacy and modern identity, but their core business is data exploitation. That contradiction is the opportunity.
What’s Actually Hard
The tech is not the hardest part. Zero-knowledge proofs, decentralized identifiers, biometrics — the building blocks are there.
The hard part is the sales cycle.
You are not selling software. You are selling trust. You are selling a promise that your system is more secure, more compliant, and more reliable than the status quo. Your buyer isn’t a product manager looking for a cool feature. Your buyer is a Chief Information Security Officer or a General Counsel.
Their first question isn’t “How does it work?”. It’s “Who do we sue if this goes wrong?”.
You are asking enormous, risk-averse organisations to rip out a core piece of their infrastructure — how they know who their customers are — and replace it with yours. This involves navigating procurement hell, legal reviews, and security audits that can take 18 months or more. You don’t win with a better demo. You win with better liability terms, better compliance certifications, and a story about risk reduction that the board can understand.
What’s Shipping Now
The most interesting work today is happening at the infrastructure layer, with founders who have learned the lessons of the past. They’re not building another social network with a new login. They’re building the pipes.
Killing the Password: Startups are finally tackling the original sin. Beyond Identity is pushing passwordless authentication using device-bound cryptographic keys, making phishing nearly impossible. 1Kosmos combines biometrics with a private blockchain to prove identity without storing centralised credentials.
Building Reusable Identity: The dream of a single, portable identity is getting closer. ID.me has carved out a huge niche with government agencies, offering a reusable login for accessing public services. On the decentralized front, Civic and SelfKey are using blockchain to build user-controlled identity systems.
Delivering Dev Tools: The smartest founders know that developers choose the next generation of infrastructure. uPort, now evolved into projects like Veramo, provides open-source tools for building with decentralized identity. In Web3, Privy is giving developers simple APIs to embed wallets and authentication into their apps, abstracting away the complexity.
Where This Goes
The noise and fragmentation are signs of an underlying convergence. Privacy, identity, and AI governance are not three separate markets. They are becoming one single problem: how do you establish and manage trust in a digital world?
The next 36 months will be a race to build the integrated “trust infrastructure” that solves this.
The bet is that a startup, unburdened by legacy tech and siloed business units, can build this unified platform faster and better than the incumbents who are trying to bolt these pieces together. The winner won’t just offer passwordless login, or a consent dashboard, or an AI governance report. They will offer a single platform that manages the entire lifecycle of digital trust for an enterprise.
This is an infrastructure play. The exits will look less like consumer apps and more like the $96 billion in cybersecurity M&A we saw in 2025 — strategic acquisitions by major cloud and security players.
Moves Worth Stealing
Ride the Regulatory Wave (The OneTrust Play): Don’t wait for demand to appear. Find the next GDPR-level event — a new AI liability law, a federal privacy bill — and build the tool that makes compliance automatic. Sell certainty to lawyers.
Become Essential Infrastructure (The Securiti AI Play): Don’t try to be everything. Build one critical component of the trust stack so well that a larger platform like Veeam, Microsoft, or Salesforce has no choice but to acquire you. Be the definitive solution for one piece of the puzzle.
Solve the Original Pain (The Beyond Identity Play): Go back to first principles. The password is a 60-year-old hack. Find the root of the problem that everyone else is just managing and build the thing that eliminates it entirely.
The Why Now
Three forces are creating a brief window of opportunity.
AI Creates New Urgency: The explosion of AI makes data governance and identity verification a C-suite priority. The old tools aren’t equipped to manage AI models, training data, and the new attack vectors they create.
Regulation is Expanding: The compliance wave that started with GDPR is now global and expanding to include AI. This creates new, mandatory budget items inside every large company.
The Incumbents are Buying: The record-breaking M&A in cybersecurity shows that the big players are acquiring innovation, not building it. This provides a clear path to exit for startups that can build something valuable.
The convergence of these forces means that for the first time, there is both the budget and the urgency to finally fix the internet’s broken identity layer.
If You’re Starting Monday
The Wedge: Don’t build a generic identity platform. Pick a single, painful, high-stakes verification problem in one regulated industry. Example: proving the identity of participants in decentralised clinical trials for a pharma company.
The Trap: Building a consumer-first “digital wallet” for identity. You will burn millions trying to solve a two-sided market problem and get crushed by platform players. Sell to the enterprise. They have the problem and the money.
The Customer: The Chief Information Security Officer (CISO) or the Chief Compliance Officer. The person who gets fired when a data breach or an AI audit goes wrong.
The First Hire: Your first hire should not be a growth hacker. Your first hire should be a lawyer who has spent years advising companies on data privacy and AI ethics. Your product is not just code; it’s a manifestation of legal and ethical rules.
Go Deeper
Momentum Cyber 2025 Report: Analysis of the record $96B in cybersecurity M&A. (Link)
The Information on OneTrust: The inside story of the compliance gold rush and market consolidation. (Link)
TransUnion 2025 Earnings: How incumbents are using AI to drive growth. (Link)
Rothschild & Co on AI Investment: Data on the 2025 venture capital boom driven by AI. (Link)
Contrary Research on OneTrust: A breakdown of the platform serving 75% of the Fortune 100. (Link)
For the ❤️ of startups
Arthur is the AI native startup operating system I’m building in public — not hype, but a system that turns input into structured execution and tracks founder progress. If you want to follow or use it, it’s open for early access.
→ Access Arthur
Thank you for reading. If you liked it, share it with your friends, colleagues and everyone interested in the startup Investor ecosystem.
If you’ve got suggestions, an article, research, your tech stack, or a job listing you want featured, just let me know! I’m keen to include it in the upcoming edition.
Please let me know what you think of it, love a feedback loop 🙏🏼
🛑 Get a different job.
Subscribe and follow me on LinkedIn or Twitter to never miss an update.